Here, We provide Wireless Communication GTU Paper Solution Winter 2022. Read the Full DS GTU paper solution given below.
Wireless Communication GTU Old Paper Winter 2022 [Marks : 70] : Click Here
(a) Define Cellular network. Explain it with its architecture.
A cellular network is a wireless communication network that allows mobile devices to communicate with each other and with the internet by using radio waves transmitted through cellular towers or base stations. This technology is the foundation for mobile phone communication and data transfer.
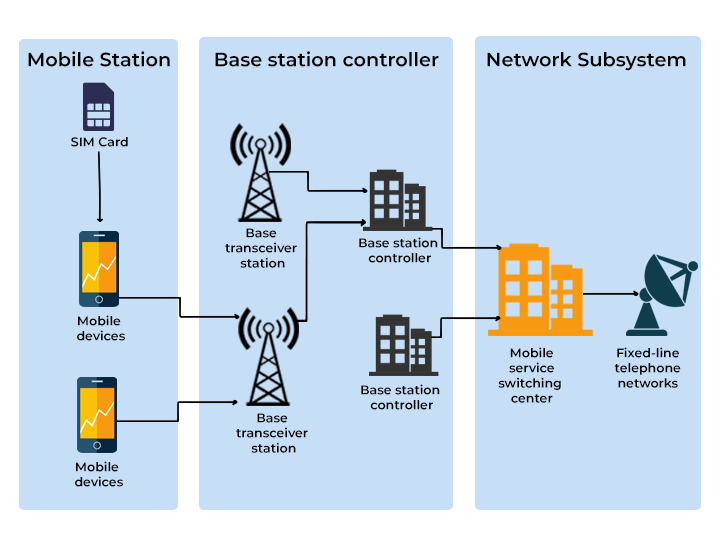
The architecture of a cellular network consists of three main components:
- Mobile Station (MS): This is the mobile device that connects to the cellular network. It includes the hardware and software necessary to communicate with the network.
- Base Station Subsystem (BSS): The BSS is composed of two components: the Base Transceiver Station (BTS) and the Base Station Controller (BSC). The BTS is responsible for sending and receiving radio signals from the MS, while the BSC manages the communication between the BTS and the Mobile Switching Center (MSC).
- Network Subsystem (NSS): The NSS is composed of two main components: the MSC and the Home Location Register (HLR). The MSC is responsible for routing calls and messages between different MSs or between an MS and a landline telephone. The HLR is a database that stores information about each MS, including its phone number and location.
(b) Explain any three different type of generation (1G to 5G) used in
wireless system with its advantages and disadvantages.
1G, 2G, 3G, 4G, and 5G are the five generations of wireless communication technologies. Each generation represents significant advancements in wireless communication technology. Here’s a brief explanation of the different generations and their advantages and disadvantages:
1G: 1G stands for the first generation of mobile communication technology that was introduced in the 1980s. It was an analog communication technology that allowed voice communication only. The main advantages of 1G are that it paved the way for mobile communication and made wireless communication possible. However, it had many disadvantages such as poor voice quality, low capacity, and limited features.
2G: 2G stands for the second generation of mobile communication technology that was introduced in the 1990s. It was a digital communication technology that allowed voice and data communication. The main advantages of 2G are that it provided better voice quality, higher capacity, and added features like text messaging. However, it had a disadvantage of low data transfer rates.
3G: 3G stands for the third generation of mobile communication technology that was introduced in the early 2000s. It was a digital communication technology that allowed high-speed data transfer, including video calling and mobile internet access. The main advantages of 3G are that it provided faster data transfer rates, improved voice quality, and the ability to send multimedia messages. However, it had a disadvantage of high power consumption.
4G: 4G stands for the fourth generation of mobile communication technology that was introduced in the late 2000s. It was an all-IP based technology that allowed for even faster data transfer rates, high-quality video streaming, and advanced features such as voice over LTE (VoLTE). The main advantages of 4G are that it provided faster data transfer rates, improved voice quality, and the ability to send and receive multimedia messages. However, it had a disadvantage of limited coverage in remote areas.
5G: 5G stands for the fifth generation of mobile communication technology that was introduced in the late 2010s. It is an all-IP based technology that allows for faster data transfer rates, lower latency, and massive device connectivity. The main advantages of 5G are that it provides faster data transfer rates, higher capacity, and the ability to connect more devices simultaneously. However, it has a disadvantage of higher deployment costs and limited availability in some areas.
(c) Illustration of how 120 degree sectoring reduces interference from co-
channel cells. Out of the 6 co-channel cells in the first tier, only 2 of
them interfere with the center cell. If Omni-directional antennas were
used at each base station, all 6 co-channel cells would interfere with the
center cell.
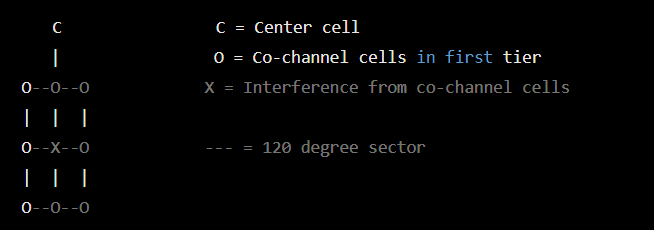
In the diagram above, there are 7 cells in total, with the center cell denoted by C. The cells denoted by O are the co-channel cells in the first tier, which share the same frequency with the center cell.
If omni-directional antennas were used at each base station, all 6 co-channel cells would interfere with the center cell, resulting in poor call quality and dropped calls. However, by using 120 degree sectoring, only 2 of the co-channel cells interfere with the center cell, as denoted by the X marks.
The 120 degree sectoring refers to the directional antenna used in each base station, which divides the coverage area into three 120 degree sectors. This reduces interference from co-channel cells in adjacent sectors and improves the overall quality of the wireless network.
(a) Define WLAN. Also explain it with its topology.
WLAN stands for Wireless Local Area Network. It is a type of computer network that uses wireless data connections between devices, such as laptops, smartphones, and tablets, to provide network communication within a limited geographic area.
The topology of WLAN can be one of the following:
- Ad-hoc mode: In this mode, devices communicate directly with each other without the need for a central access point. This type of topology is often used in peer-to-peer networking scenarios.
- Infrastructure mode: In this mode, devices communicate with each other through a central access point or a wireless router. The access point acts as a bridge between the wireless devices and the wired network.
- Mesh mode: In this mode, devices communicate with each other through a network of access points, forming a mesh network. Each access point acts as a node, and the network can be extended by adding more access points.
In all of these topologies, wireless devices communicate with each other using radio frequency (RF) signals. The RF signals are sent and received by the wireless network interface cards (NICs) installed in the devices. The access points and routers act as bridges between the wireless devices and the wired network, enabling wireless devices to access network resources, such as the Internet and shared files and printers.
(b) How many types of techniques used in WLL? Explain.
WLL stands for Wireless Local Loop, which is a wireless communication system that replaces the traditional copper-wire telephone connections between the telephone exchange and the customer premises. There are two types of techniques used in WLL, which are as follows:
- Fixed Wireless Access (FWA): In this technique, the customer premises are equipped with a fixed wireless terminal (FWT), which is connected to the telephone network via a base station. The FWT acts as a bridge between the customer premises and the base station, which provides wireless connectivity between the two. The base station is connected to the telephone exchange, which provides connectivity to the public switched telephone network (PSTN). The FWA system can support both voice and data services, and it is suitable for areas where it is not feasible to lay copper-wire cables.
- Cordless Telephony: In this technique, the customer premises are equipped with a cordless telephone set, which communicates with a base station via radio frequency signals. The base station is connected to the telephone network, which provides connectivity to the PSTN. The cordless telephony system is suitable for small office/home office (SOHO) environments, where a single base station can provide wireless connectivity to multiple cordless telephone sets. The system can support both voice and data services, and it provides mobility within a limited range of the base station.
Both FWA and cordless telephony techniques provide wireless connectivity to the customer premises, which eliminates the need for copper-wire cables. These techniques are suitable for areas where it is not feasible to lay cables, such as rural areas or densely populated urban areas, where it is difficult to lay cables due to space constraints. However, these techniques have some limitations, such as limited coverage range, susceptibility to interference from other wireless devices, and limited bandwidth for data services.
(c) Design 802.11 architecture of an infrastructure network.
An 802.11 infrastructure network consists of at least one access point (AP) and one or more wireless clients. The AP acts as the central point of communication for the wireless network, managing communication between the wireless clients and other network resources. The basic architecture of an 802.11 infrastructure network is as follows:
- Wireless Clients: The wireless clients are the devices that connect to the wireless network. These clients can be laptops, mobile phones, tablets, or any other device with a wireless network interface card (NIC).
- Access Point (AP): The access point is a wireless networking device that acts as a bridge between wireless clients and a wired network. It receives data from wireless clients and forwards it to the wired network, and vice versa.
- Wireless Distribution System (WDS): WDS is used to interconnect APs, allowing wireless clients to seamlessly roam between APs while maintaining a stable network connection.
- Backbone Network: The backbone network is the wired network infrastructure that provides connectivity between the APs and other network resources, such as servers and the internet.
The topology of an 802.11 infrastructure network is typically a star topology, with the AP acting as the central hub. The wireless clients connect to the AP through a wireless connection, and the AP is connected to the backbone network through a wired connection. The WDS interconnects the APs to allow wireless clients to move between APs while maintaining their network connection.
(c) Design 802.11 architecture of an ad-hoc network.
An ad-hoc network is a wireless network in which devices communicate with each other directly without any centralized infrastructure. The 802.11 standard provides support for ad-hoc networks, which are also known as Independent Basic Service Set (IBSS) networks.
The architecture of an 802.11 ad-hoc network consists of the following components:
- Wireless Nodes: The devices or computers that connect to the ad-hoc network wirelessly are called wireless nodes. These nodes communicate with each other directly without any centralized infrastructure.
- Network Interface Card (NIC): Each wireless node should have a wireless NIC that supports the 802.11 standard. The NIC is responsible for transmitting and receiving data over the wireless medium.
- Wireless Channels: An ad-hoc network uses the same frequency band as other nearby wireless networks, which can cause interference. The 802.11 standard provides for multiple channels to be used in ad-hoc networks to minimize interference. Each channel can be used by only one ad-hoc network at a time.
- Basic Service Set (BSS): In an ad-hoc network, each wireless node communicates with other nodes directly. A BSS is a group of wireless nodes that can communicate with each other directly.
- Independent Basic Service Set (IBSS): An IBSS is a BSS in which all wireless nodes communicate with each other directly without any centralized infrastructure.
The architecture of an 802.11 ad-hoc network can be represented using the following diagram:
+------+
| Node |
+------+
|
|
|
+------+
| Node |
+------+
/ \
/ \
/ \
+------+ +------+
| Node | | Node |
+------+ +------+
In this diagram, each box represents a wireless node and the lines connecting them represent direct communication between the nodes. There is no centralized infrastructure in this network, and each node communicates directly with other nodes in the network.
(a) Why we use hexagon shape in cell structure? Give the proper reason.
The hexagon shape is used in the cell structure of cellular networks due to several reasons:
- Coverage area: The hexagon shape provides the largest coverage area of any regular polygon with the same perimeter. Thus, by using hexagonal cells, the coverage area of a cellular network can be maximized while minimizing the number of cells required.
- Minimum overlap: When hexagonal cells are used, the cells can be arranged in a way that minimizes overlap and reduces interference between cells. This results in more efficient use of the available frequency spectrum.
- Ease of network planning: Hexagonal cells are easy to plan and configure for network engineers. The regular shape and symmetry of the cells make it easier to predict and model radio propagation characteristics, which helps in designing a more efficient network.
- Simplification of handoff procedures: Hexagonal cells make handoff procedures simpler and more efficient. As the cells are regular in shape and have equal sides, it is easier to determine when a mobile device needs to handoff to another cell.
(b) Clarify how we increase cluster size and cell capacity in cellular
network.
In a cellular network, the cluster size refers to the number of cells in a group. Increasing the cluster size can improve the capacity of the network, as it reduces the number of control channels required to manage the cells in the cluster. This allows for more efficient use of the available frequencies, as each control channel requires a certain amount of bandwidth.
To increase the cluster size, the following steps can be taken:
- Reduce the number of frequency reuse patterns: In a cellular network, each cell is assigned a set of frequencies for communication. The same set of frequencies can be reused in other cells, but they must be far enough apart to avoid interference. By reducing the number of frequency reuse patterns, the same set of frequencies can be used in more cells, increasing the cluster size.
- Increase the transmit power of the base stations: By increasing the transmit power of the base stations, the coverage area of each cell can be expanded. This allows for more cells to be grouped together in a cluster.
- Use directional antennas: Directional antennas can be used to concentrate the radio frequency (RF) energy in a specific direction. This allows for more efficient use of the available frequencies and can increase the coverage area of each cell. By increasing the coverage area of each cell, more cells can be grouped together in a cluster.
Increasing the cell capacity can also be achieved by implementing various techniques such as:
- Sectorization: In sectorization, each cell is divided into smaller sectors, each with its own antenna. This allows for more efficient use of the available frequencies, as the same set of frequencies can be reused in each sector.
- Microcell deployment: By deploying smaller cells within a larger cell, the capacity of the network can be increased. This is particularly useful in high-density areas, where a large number of users are competing for network resources.
- Frequency reuse: Frequency reuse is a technique where the same set of frequencies is used in multiple cells, but the cells must be far enough apart to avoid interference. By reusing the same frequencies, more users can be accommodated within a given area, increasing the cell capacity.
(c) What is frequency reuse? Explain it with proper figure.
Frequency reuse is a technique used in cellular networks to increase the capacity of the network by reusing the same set of radio frequencies in different cells, while minimizing interference between them. In frequency reuse, a group of radio channels are allocated to a cluster of cells, and then the same group of channels are reused in another cluster of cells, but at a sufficient distance to minimize interference.
The most common frequency reuse pattern is the 7-cell reuse pattern, which uses a hexagonal cell structure. In this pattern, a group of seven cells reuse the same set of radio frequencies, as shown in the figure below:
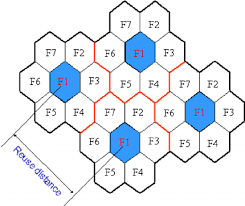
The central cell in the group uses all available frequencies, while the surrounding six cells reuse a subset of the frequencies, typically every seventh frequency. This ensures that each cell has enough frequencies to handle the traffic demands while minimizing interference from adjacent cells that use the same frequencies.
By reusing frequencies in different cells, the total number of available frequencies can be shared among more cells, resulting in an increase in the capacity of the network. However, the trade-off is that the distance between the cells that reuse the same frequencies must be sufficient to avoid interference.
OR
(a) Give proper reason of difference between co-channel interference and
adjust channel interference.
Co-channel interference occurs when two or more cells in a cellular network use the same frequency channels for communication, resulting in signal interference and degraded call quality. This is because the signals from these cells interfere with each other, causing noise and distortion in the received signals.
On the other hand, adjacent channel interference occurs when cells use frequency channels that are close to each other, resulting in interference between the signals. This is because the signals from these cells overlap in the frequency domain, causing signal distortion and increased noise in the received signals.
The main reason for the difference between co-channel interference and adjacent channel interference is the frequency separation between the channels used by the cells. In co-channel interference, the same frequency channel is used by multiple cells, while in adjacent channel interference, the frequency channels used by the cells are close to each other, but not the same. The frequency separation between the channels determines the degree of interference between them, with closer channels causing more interference.
(b) Explain handoff process and dwell time.
Handoff is the process of transferring an ongoing call or data session from one cell to another while a user is moving in a cellular network. The handoff process is required to maintain the continuity of the communication without any interruption or loss of quality. The dwell time is the minimum amount of time that a mobile device must stay in a cell before it can switch to another cell.
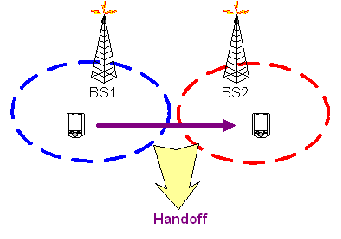
The handoff process includes the following steps:
- Signal strength measurement: The mobile device continuously measures the signal strength of the current cell and the neighboring cells.
- Threshold comparison: When the signal strength of the neighboring cell exceeds a certain threshold value, the mobile device sends a request for handoff to the base station of the current cell.
- Allocation of resources: The base station of the new cell allocates the necessary resources for the handoff, such as a radio channel and time slot.
- Connection setup: The mobile device switches to the new channel and time slot to establish a connection with the base station of the new cell.
- Handoff completion: The mobile device sends a confirmation message to the base station of the new cell, and the old connection is released.
The dwell time is the minimum time that a mobile device must remain in a cell before it can initiate a handoff. The dwell time is determined by the speed of the mobile device and the size of the cell. A smaller cell requires a shorter dwell time, while a larger cell requires a longer dwell time. The purpose of the dwell time is to avoid unnecessary handoffs that can cause network congestion and reduce the quality of service.
(c) Explain concept of co-channel cells with its geometry.
Co-channel cells are the cells that use the same frequency channel to communicate with mobile devices. In a cellular network, it is common for adjacent cells to use the same frequency channel, which can lead to interference and reduced quality of service. The geometry of co-channel cells can be visualized using a hexagonal cell layout, which is the most common arrangement used in cellular networks.
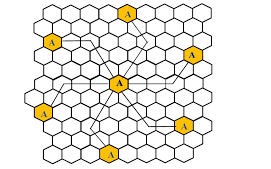
In a hexagonal cell layout, each cell is surrounded by six adjacent cells. If the adjacent cells use the same frequency channel, interference can occur at the boundary of the cells, which is referred to as the cell edge. The interference can cause signal degradation and dropped calls, which can lead to a poor user experience.
To minimize co-channel interference, cellular networks use techniques such as frequency reuse, where frequency channels are reused in non-adjacent cells, and cell sectoring, where cells are divided into smaller sectors to reduce the number of adjacent cells using the same frequency channel. These techniques help to increase capacity and improve the quality of service in cellular networks.
(a) Define Radio Propagation. Explain Path- loss of NLOS and LOS
systems.
Radio propagation refers to the behavior of radio waves as they travel through space. It involves the study of how radio waves propagate through different environments, such as air, water, buildings, and other obstacles. Understanding radio propagation is essential for designing and optimizing wireless communication systems.
Path loss refers to the reduction in power density of an electromagnetic wave as it propagates through space. Path loss occurs due to various factors, including distance, attenuation, reflection, diffraction, and scattering.
NLOS (Non-Line of Sight) path loss occurs when the radio wave encounters obstacles such as buildings, trees, or other obstructions that block or reflect the signal. The signal strength decreases rapidly with increasing distance due to the absorption, reflection, and scattering of the signal by the obstacles.
LOS (Line of Sight) path loss occurs when there is a clear line of sight between the transmitter and receiver, with no obstructions or reflections. The signal strength decreases with distance, but at a slower rate than NLOS. The path loss in an LOS system can be modeled using the Friis transmission formula, which relates the received power to the transmitted power, frequency, distance, and other parameters.
(b) What is CSMA Protocols? Explain briefly.
CSMA (Carrier Sense Multiple Access) protocol is a method used in computer networks to regulate access to a shared communication medium. The main idea behind CSMA is that a device should check the communication medium for activity before transmitting data.
There are three types of CSMA protocols:
- CSMA/CD (Carrier Sense Multiple Access/Collision Detection): This protocol is used in wired Ethernet networks. When a device wants to transmit data, it listens to the communication medium. If the medium is idle, it begins transmitting. If the medium is busy, the device waits and retries after a random amount of time. If two devices transmit at the same time, a collision occurs and both devices stop transmitting. They then wait for a random amount of time and retry.
- CSMA/CA (Carrier Sense Multiple Access/Collision Avoidance): This protocol is used in wireless networks. In this protocol, a device listens to the communication medium before transmitting data. If the medium is idle, it transmits. If the medium is busy, it waits for a random amount of time before retrying. This protocol also includes an acknowledgement mechanism to confirm successful data transmission.
- CSMA/CR (Carrier Sense Multiple Access/Contention Resolution): This protocol is used in networks with a large number of devices. In this protocol, devices compete for access to the communication medium by sending a request-to-send (RTS) frame. The receiving device sends a clear-to-send (CTS) frame to the sender, allowing it to transmit data. This protocol reduces collisions and improves network performance.
(c) Explain TDMA and CDMA with example.
TDMA (Time Division Multiple Access) and CDMA (Code Division Multiple Access) are two popular multiple access techniques used in wireless communication systems.
TDMA is a digital transmission technology that allows multiple users to share the same frequency channel by dividing the signal into different time slots. In TDMA, each user is assigned a unique time slot within a given frequency band. During this time slot, the user transmits its data. This technique is commonly used in cellular phone systems.
For example, consider a TDMA system with four users sharing a frequency channel. Each user is assigned a unique time slot within a given frame. The frame duration is divided into four equal time slots, and each user transmits during its assigned time slot. In the diagram below, User 1 transmits during time slot 1, User 2 transmits during time slot 2, and so on.

CDMA is a digital transmission technology that allows multiple users to share the same frequency channel by assigning a unique code to each user. In CDMA, each user is assigned a unique code, which is used to spread the signal over a wide frequency band. The receiver uses the same code to extract the signal from the noise.
For example, consider a CDMA system with three users sharing a frequency channel. Each user is assigned a unique code, which is used to spread the signal. When User 1 transmits its data, the data is spread over the entire frequency band using its unique code. The same is done for User 2 and User 3. The receiver uses the same code to extract the signal from the noise.
OR
(a) Define fading. Explain it with its types.
In wireless communication, fading refers to the phenomenon where the signal strength of a transmitted signal is reduced due to various factors such as multipath propagation, scattering, and absorption. The reduction in signal strength can lead to errors in the received signal, which can result in a loss of data or reduced quality of the communication.
There are two main types of fading:
- Small-scale fading: It is caused by the changes in the signal strength due to multipath propagation. The signal strength can vary significantly over short distances, and it can change rapidly over time. This type of fading can be further divided into two categories:
- Rayleigh fading: It occurs when there is no dominant path in the channel. The signal is scattered in all directions, and there is no direct line-of-sight path between the transmitter and receiver. The signal strength follows a Rayleigh distribution, which means that it is characterized by rapid fluctuations.
- Rician fading: It occurs when there is a dominant path in the channel in addition to the scattered paths. The signal strength follows a Rician distribution, which means that it has a dominant component and a random component.
- Large-scale fading: It is caused by the attenuation of the signal due to the distance between the transmitter and receiver. The signal strength decreases as the distance between the transmitter and receiver increases. This type of fading is also known as path loss and can be further divided into two categories:
- LOS (Line-of-sight) path loss: It occurs when there is a clear line-of-sight path between the transmitter and receiver. The signal strength decreases with the distance, and it follows the inverse-square law.
- NLOS (Non-line-of-sight) path loss: It occurs when there are obstacles between the transmitter and receiver, such as buildings, trees, or hills. The signal strength is affected by the type and number of obstacles, as well as the frequency of the signal.
(b) Define Multiple Access Techniques. Compare it.
Multiple Access Techniques are methods used to allow multiple users to share a common communication channel. There are several Multiple Access Techniques, including Frequency Division Multiple Access (FDMA), Time Division Multiple Access (TDMA), Code Division Multiple Access (CDMA), and Orthogonal Frequency Division Multiple Access (OFDMA).
FDMA divides the available bandwidth into frequency bands, and each user is assigned a unique frequency band for transmission. TDMA divides the time into time slots, and each user is assigned a unique time slot for transmission. CDMA uses unique codes to differentiate between users, allowing multiple users to transmit on the same frequency at the same time. OFDMA uses multiple orthogonal sub-carriers to transmit multiple data streams in parallel.
FDMA is best suited for analog systems, where bandwidth is allocated to users. TDMA is best suited for digital systems, where time slots are allocated to users. CDMA is suitable for both analog and digital systems, but requires complex encoding and decoding techniques. OFDMA is most suitable for high-speed data transmission and is used in modern cellular systems.
In comparison, FDMA provides fixed bandwidth allocation, while TDMA provides fixed time allocation. CDMA allows for flexible bandwidth allocation, while OFDMA provides flexible bandwidth and time allocation. In terms of spectral efficiency, CDMA and OFDMA offer higher spectral efficiency compared to FDMA and TDMA. However, CDMA and OFDMA require more complex hardware and signal processing techniques.
(c) Explain FDMA and OFDM with example.
FDMA (Frequency Division Multiple Access) and OFDM (Orthogonal Frequency Division Multiplexing) are two multiple access techniques used in wireless communication.
FDMA is a method of dividing the available frequency spectrum into multiple non-overlapping frequency bands or channels. Each user is assigned a separate frequency band for transmitting and receiving data. For example, in an analog radio system, different stations use different frequencies for transmission. In a digital system, each channel can be divided into multiple time slots, and each user can transmit during their allocated time slot.
On the other hand, OFDM is a digital modulation technique that divides the available frequency spectrum into multiple subcarriers. The subcarriers are orthogonal to each other, which means they do not interfere with each other. This allows for efficient use of the frequency spectrum and reduces the effects of multipath fading.
For example, in Wi-Fi communication, OFDM is used to transmit data over multiple subcarriers, each with a specific frequency and phase. This allows for high-speed data transfer and robust communication, even in noisy and interference-prone environments.
In comparison, FDMA is best suited for analog systems, while OFDM is more efficient for digital systems that require high-speed data transfer and reliable communication in noisy environments. OFDM is also used in many modern communication systems such as 4G and 5G cellular networks.
(a) Define Wi-Fi, WiMAX and ZigBee Networks.
- Wi-Fi (Wireless Fidelity): It is a wireless network technology that uses radio waves to provide wireless high-speed internet and network connections. It is a popular technology used in homes, offices, and public places like airports, cafes, and hotels. Wi-Fi operates on the 2.4 GHz and 5 GHz frequency bands, and the range of the network depends on factors such as the type of antenna and the number of access points.
- WiMAX (Worldwide Interoperability for Microwave Access): It is a wireless broadband technology that provides high-speed internet access over long distances. WiMAX operates on the 2.3 GHz, 2.5 GHz, 3.5 GHz, and 5.8 GHz frequency bands, and it can provide coverage up to 50 km from a base station. WiMAX is used in rural and remote areas where wired internet infrastructure is not available.
- ZigBee: It is a low-power wireless network technology used for the Internet of Things (IoT) devices. ZigBee operates on the 2.4 GHz frequency band and provides a range of up to 100 meters. It is designed for low-data rate applications that require long battery life, such as home automation, lighting control, and smart meters. ZigBee networks are typically made up of a coordinator device, routers, and end devices.
(b) Briefly explain different types of propagation models.
Propagation models are used to predict the path of a radio signal as it travels from a transmitter to a receiver in a wireless communication system. There are various types of propagation models that are used depending on the frequency of the signal, the environment, and the distance between the transmitter and receiver. Some of the common propagation models are:
- Free Space Propagation Model: It is the simplest model and assumes that the radio signal propagates through free space without any obstruction, absorption, or reflection. The received signal power decreases with the square of the distance between the transmitter and receiver.
- Two-Ray Ground Reflection Model: It assumes that the radio signal follows two paths, one is the direct path and the other is the path that is reflected from the ground. This model is suitable for long-distance communication between a high antenna and a low antenna.
- Okumura Model: It is a statistical model that is based on extensive measurements of radio signals at different frequencies in different environments. The model takes into account the frequency of the signal, the distance between the transmitter and receiver, the height of the antennas, the terrain, and the buildings in the environment.
- Hata Model: It is a modification of the Okumura model and is widely used for urban and suburban areas. It includes additional parameters such as the frequency of the signal, the height of the antennas, the distance between the transmitter and receiver, and the type of environment.
- Ray Tracing Model: It is a complex model that uses ray tracing algorithms to simulate the propagation of radio waves in a 3D environment. This model takes into account the reflection, refraction, and diffraction of radio waves from different objects such as buildings, trees, and walls.
- Foliage Propagation Model: It is used for predicting the signal strength in areas with dense foliage such as forests. The model takes into account the type and density of foliage, the frequency of the signal, and the distance between the transmitter and receiver.
- Indoor Propagation Model: It is used for predicting the signal strength in indoor environments such as buildings, shopping malls, and airports. The model takes into account the attenuation of the signal due to walls, ceilings, floors, and other obstacles in the environment.
(c) Define GSM. Explain it with its architecture.
GSM stands for Global System for Mobile Communications. It is a standard for digital cellular communication that is widely used across the world. GSM is a second-generation (2G) technology that was developed to replace the analog first-generation (1G) systems. GSM was first introduced in Europe in 1991 and has since become the dominant mobile phone standard worldwide.
The architecture of the GSM network can be divided into three main parts: the Mobile Station (MS), the Base Station Subsystem (BSS), and the Network Switching Subsystem (NSS).
- Mobile Station (MS): The Mobile Station consists of the mobile device and the Subscriber Identity Module (SIM) card. The SIM card contains the user’s phone number, account information, and other data.
- Base Station Subsystem (BSS): The BSS is responsible for managing the radio communication between the mobile device and the network. The BSS consists of two main components:a. Base Transceiver Station (BTS): The BTS is responsible for transmitting and receiving radio signals to and from the mobile device. Each BTS covers a specific area, which is called a cell.b. Base Station Controller (BSC): The BSC controls one or more BTSs and manages the handover of calls between cells.
- Network Switching Subsystem (NSS): The NSS is responsible for managing the calls and messages within the network. The NSS consists of two main components:a. Mobile Switching Center (MSC): The MSC is the central component of the network and is responsible for routing calls and messages between the BSS and other networks.b. Home Location Register (HLR): The HLR is a database that contains information about the subscribers in the network, including their phone numbers, account information, and location.
GSM uses Time Division Multiple Access (TDMA) technology, which divides the frequency band into time slots. Each time slot can be assigned to a different call, allowing multiple users to share the same frequency band. GSM operates in several frequency bands, depending on the country and region. The most commonly used bands are 900 MHz and 1800 MHz.
OR
(a) Define Wireless Adhoc Network and Mobile Portability? Explain
briefly.
A wireless ad hoc network is a type of wireless network where nodes communicate with each other without the need for a centralized infrastructure such as an access point. The nodes in the network are responsible for routing data from source to destination. Ad hoc networks can be formed on the fly and are often used in situations where infrastructure-based networks are not available, such as disaster recovery or military operations.
Mobile portability refers to the ability of a user to maintain the same phone number and service when switching between different service providers or when moving from one geographical location to another. This allows for seamless communication even when the user is on the move. Mobile portability is facilitated by the use of SIM cards which store the user’s identity and service information.
(b) Explain Spread Spectrum with its types.
Spread spectrum is a technique used in wireless communication systems to spread the bandwidth of a signal over a larger frequency range than the minimum bandwidth required. The primary goal of this technique is to reduce interference from other signals on the same frequency band and to increase the security of the communication channel. There are two types of Spread Spectrum techniques: Direct Sequence Spread Spectrum (DSSS) and Frequency Hopping Spread Spectrum (FHSS).
- Direct Sequence Spread Spectrum (DSSS):
DSSS works by spreading the signal over a wide frequency band by multiplying the data signal by a pseudo-random bit sequence known as a “chipping code.” This chipping code is generated by a pseudo-random sequence generator and is used to modulate a higher frequency carrier signal. The modulated signal is then spread over a wider frequency range, making it more resistant to interference. The receiver de-spreads the signal by multiplying it by the same chipping code and then integrating the result over a specific time period to recover the original data signal. DSSS is used in wireless LANs, Bluetooth, and CDMA (Code Division Multiple Access) cellular systems.
- Frequency Hopping Spread Spectrum (FHSS):
FHSS works by rapidly switching the carrier frequency of the transmitted signal between multiple channels in a pre-determined sequence. This sequence is known to both the transmitter and the receiver. The hopping rate can be fixed or adaptive, and the frequency of the hopping sequence can be controlled. This technique makes the signal more resilient to interference because any interference on a single frequency will only affect a small portion of the transmitted data. FHSS is used in Bluetooth, wireless LANs, and military communications.
(c) Define GPRS. Explain it with its architecture.
GPRS stands for General Packet Radio Service, which is a packet-switched wireless communication service that allows mobile devices to transmit and receive data over a cellular network. GPRS is the first 2.5G mobile data standard and is considered a precursor to 3G and 4G mobile data networks.
The architecture of GPRS consists of three main components: mobile stations (MS), base stations (BS), and the GPRS core network. The mobile station is the end-user device that communicates with the base station over the air interface. The base station is responsible for managing the radio resources and handling the transmission of data between the mobile station and the GPRS core network.
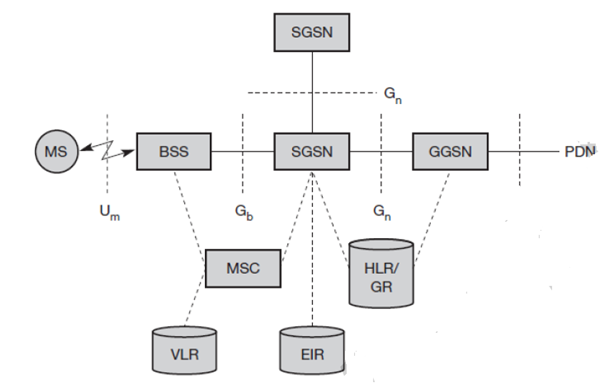
The GPRS core network consists of several components, including the Serving GPRS Support Node (SGSN), Gateway GPRS Support Node (GGSN), and Home Location Register (HLR). The SGSN is responsible for managing the communication between the mobile station and the GGSN, which is the entry and exit point for all GPRS data traffic to and from external networks such as the internet. The HLR stores subscriber information, including subscriber profiles and authentication information.
GPRS uses a packet-switched network architecture, which means that data is transmitted in small packets over the network. Each packet is routed individually to its destination based on the packet header information, allowing for more efficient use of network resources and faster data transmission speeds. GPRS also uses a shared air interface, which means that multiple mobile devices can share the same frequency channel, improving the network’s capacity and efficiency.
“Do you have the answer to any of the questions provided on our website? If so, please let us know by providing the question number and your answer in the space provided below. We appreciate your contributions to helping other students succeed.”
