Here, We provide Cryptography and Network Security GTU Paper Solution Winter 2022. Read the Full CNS GTU paper solution given below. Cryptography and Network Security GTU Old Paper Winter 2022 [Marks : 70] : Click Here
(a) Explain the following terms in brief:
i) Confidentiality
ii) Non-repudiation
iii) Access Control.
i) Confidentiality: Confidentiality refers to the protection of sensitive or confidential information from unauthorized access, use, or disclosure. It ensures that only authorized individuals or entities have access to confidential data, and that it is kept secure and confidential. Confidentiality is an important aspect of information security and is typically achieved through various security measures such as encryption, access controls, and data classification. For example, in a healthcare setting, patient medical records are considered confidential and should only be accessed by authorized healthcare professionals for legitimate purposes.
ii) Non-repudiation: Non-repudiation is the assurance that the originator of a message or transaction cannot deny their involvement or repudiate the authenticity of the message or transaction. It provides evidence that a message or transaction was sent or received by a specific entity, and that entity cannot later deny their involvement. Non-repudiation is important in digital communication and transactions to prevent disputes and ensure trust among parties. For example, in digital signatures, non-repudiation ensures that the signer of a document cannot later deny their signature, providing legal validity and accountability.
iii) Access Control: Access control refers to the process of granting or denying permissions or privileges to users or entities based on their authenticated identity and authorized role. Access control ensures that only authorized users have appropriate access to resources, systems, or data, while preventing unauthorized access. Access control can be implemented through various mechanisms, such as role-based access control (RBAC), mandatory access control (MAC), discretionary access control (DAC), and others. It is a fundamental security measure used to protect information systems and prevent unauthorized access, data breaches, and information misuse.
(b) Construct a Play fair matrix with the key “Trust” and encrypt the
message “Be confident in yourself”.
Step 1: Construct the Playfair Matrix with the Key “Trust”
The Playfair matrix is a 5×5 matrix that contains unique alphabetic characters, usually excluding the letter ‘J’. Here’s how the Playfair matrix is constructed with the key “Trust”:
| T | R | U | S | T |
|---|---|---|---|---|
| U | A | B | C | D |
| E | F | G | H | I |
| K | L | M | N | O |
| P | Q | V | W | X |
Step 2: Prepare the Message for Encryption
The message “Be confident in yourself” is prepared for encryption by removing any spaces and punctuation, and converting all the letters to uppercase:
BECONFIDENTINYOURSELF
Step 3: Encrypt the Message Using the Playfair Matrix
To encrypt the message, we will use the following rules:
- If two letters of a pair are in the same row of the Playfair matrix, replace them with the letters to their right, wrapping around to the leftmost letter if needed.
- If two letters of a pair are in the same column of the Playfair matrix, replace them with the letters below them, wrapping around to the top letter if needed.
- If two letters of a pair are in different rows and columns of the Playfair matrix, replace them with the letters that are in the same row but in the column of the other letter of the pair.
Here’s how the message “BECONFIDENTINYOURSELF” is encrypted using the Playfair matrix:
| B | E | C | O | N | | F | I | D | E | N | | T | I | N | Y | O | | U | R | S | E | L | | F | | I | E | | R | | S | X | | T | | | | | ————— | | | BE | CO | NF | ID | EN | TI | NY | OU | RS | EL | F
So the encrypted message using the Playfair matrix with the key “Trust” would be: “BECOINFIDNTINYOURSSELFX”. Note that ‘X’ is added at the end to make the message length even, as Playfair encryption requires pairs of letters.
(c) List down various modes of operations of block cipher and explain any
three of them briefly.
Block ciphers operate on fixed-size blocks of data, typically in units of 64 or 128 bits. There are several modes of operation for block ciphers that define how multiple blocks of data are processed. Some of the commonly used modes of operation are:
- Electronic Codebook (ECB) mode: In this mode, each block of plaintext is encrypted independently using the same key. The same plaintext block will always produce the same ciphertext block, which may result in lack of confidentiality if the same plaintext blocks are repeated in the message. ECB mode is simple and efficient, but it does not provide good security for large messages or messages with patterns.
- Cipher Block Chaining (CBC) mode: In this mode, each plaintext block is XORed with the ciphertext of the previous block before encryption, except for the first block which is XORed with an initialization vector (IV). This adds a form of feedback to the encryption process and prevents the same plaintext blocks from producing the same ciphertext blocks. CBC mode provides better security than ECB mode, as it introduces diffusion and makes it more resistant to patterns in the plaintext.
- Counter (CTR) mode: In this mode, a counter is used as the input to the block cipher, and the counter values are encrypted to generate the keystream. The keystream is then XORed with the plaintext to produce the ciphertext. CTR mode allows for parallel encryption and decryption, as the counter values can be precomputed. It also provides a random-like access pattern to the blocks of ciphertext, making it suitable for applications that require random access to encrypted data, such as disk encryption.
- Galois/Counter Mode (GCM): This is an authenticated encryption mode that combines the Counter (CTR) mode with a Galois field multiplication for integrity protection. It provides both confidentiality and integrity, ensuring that the ciphertext is not tampered with during transmission. GCM is widely used in secure communication protocols, such as TLS, because of its efficient and secure nature.
- Output Feedback (OFB) mode: In this mode, the ciphertext of the previous block is XORed with the input to the block cipher to produce the keystream, which is then XORed with the plaintext to produce the ciphertext. OFB mode allows for error propagation, as a single bit error in the ciphertext only affects the corresponding bit in the plaintext, without affecting the rest of the ciphertext. However, it does not provide authentication or integrity protection.
(a) Encrypt the message “Coronavirus” using the Hill Cipher with the key-
[5 2]
[1 7]
Key:
[5 2]
[1 7]
We first need to convert the plaintext message into a matrix of numbers based on a substitution table. Let’s assume the substitution table is as follows:
Substitution Table:
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25
Using the substitution table, we can convert the plaintext message “Coronavirus” into a matrix of numbers:
Plaintext:
C O R O N A V I R U S
2 14 17 14 13 0 21 8 17 20 18
Next, we multiply the plaintext matrix with the key matrix (mod 26) to obtain the ciphertext matrix:
[5 2] [2 14 17 14 13 0 21 8 17 20 18] [83 156 197 156 127 21 193 78155 206 157] [1 7] * [5 2 2 2 13 0 21 8 17 20 18] = [86 113 118 84 153 14 187 49 111 135 130]
Note that we take the result modulo 26 at each step to ensure that the ciphertext matrix contains numbers within the range of 0 to 25, which corresponds to the letters in the substitution table.
The resulting ciphertext matrix is:
83 156 197 156 127 21 193 78 155 206 157
86 113 118 84 153 14 187 49 111 135 130
We can now convert the ciphertext matrix back into letters using the substitution table to obtain the encrypted message:
Ciphertext:
S A N O V V T A Y K H
So, the encrypted message using the Hill Cipher with the given key is “SANOVVTAYKH”.
(b) Differentiate Following:
i)Stream Cipher and block cipher
ii)Active attack and Passive attack
i) Stream Cipher and Block Cipher:
- Stream Cipher: A stream cipher is a type of encryption algorithm that encrypts data one bit or one byte at a time. It operates on a continuous stream of data and uses a pseudorandom key stream to encrypt the plaintext. Stream ciphers are typically faster and more efficient for encrypting data in real-time, such as in communication systems where data is transmitted continuously.
- Block Cipher: A block cipher is a type of encryption algorithm that encrypts data in fixed-size blocks, typically in chunks of 64 or 128 bits. It operates on a fixed-size block of plaintext at a time and uses a fixed-size key to encrypt the entire block. Block ciphers are typically used for encrypting large amounts of data in bulk, such as in file encryption or disk encryption.
Differences:
- Stream ciphers encrypt data one bit or one byte at a time, while block ciphers encrypt data in fixed-size blocks.
- Stream ciphers use a pseudorandom key stream, while block ciphers use a fixed-size key to encrypt entire blocks of data.
- Stream ciphers are typically faster and more efficient for encrypting data in real-time, while block ciphers are typically used for encrypting large amounts of data in bulk.
ii) Active Attack and Passive Attack:
- Active Attack: An active attack is a type of security attack where an attacker tries to modify, delete, or inject new data into a system or network to disrupt its operation or gain unauthorized access. Active attacks typically involve some form of interaction with the target system, such as sending malicious packets, injecting malware, or manipulating data in transit.
- Passive Attack: A passive attack is a type of security attack where an attacker eavesdrops or monitors communication between systems or networks without modifying or disrupting the data. Passive attacks typically involve listening to or capturing data during transmission to gain unauthorized access or obtain sensitive information without the knowledge of the communicating parties.
Differences:
- Active attacks involve modifying, deleting, or injecting new data into a system or network, while passive attacks involve eavesdropping or monitoring communication without modifying data.
- Active attacks disrupt the operation of the target system or network, while passive attacks do not disrupt data but focus on unauthorized access or data collection.
- Active attacks typically involve some form of interaction with the target system, while passive attacks do not require active interaction and are often harder to detect.
(c) Explain single round of DES algorithm.
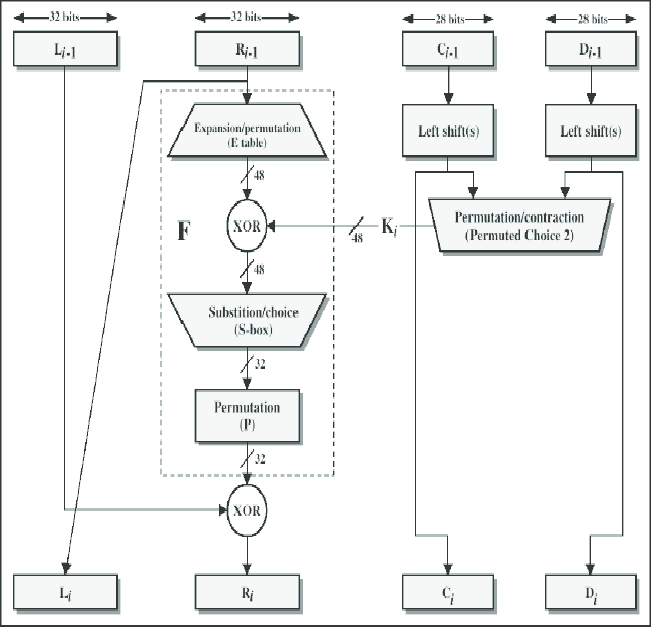
The Data Encryption Standard (DES) is a symmetric key block cipher algorithm that operates on 64-bit blocks of data and uses a 56-bit key for encryption and decryption. A single round of the DES algorithm consists of the following steps:
- Initial Permutation (IP): The 64-bit plaintext block is subjected to an initial permutation (IP) step, where the bits are rearranged according to a fixed permutation table. This step serves to provide diffusion and confusion in the plaintext.
- Key Generation: The 56-bit key is used to generate 16 subkeys, one for each round of the DES algorithm. The key is first subjected to a parity drop step, where the least significant bit of each byte is dropped, resulting in a 56-bit key. Then, the key is divided into two 28-bit halves, and each half is subjected to left circular shifts according to a pre-defined shift schedule. This generates 16 subkeys, each of which is used in a specific round of the DES algorithm.
- Subkey XOR: The 48-bit subkey for the current round is XORed with the 32-bit right half of the plaintext block obtained from the initial permutation step. This introduces the key material into the plaintext data.
- S-boxes Substitution: The 48-bit result obtained from the XOR step is divided into eight 6-bit blocks, which are then substituted using eight different S-boxes (Substitution Boxes) that are part of the DES algorithm. Each S-box takes a 6-bit input and produces a 4-bit output, based on a fixed substitution table. The S-boxes introduce non-linearity into the encryption process.
- Permutation (P-box): The 32-bit output from the S-boxes is subjected to a fixed permutation (P-box) step, which rearranges the bits according to a pre-defined permutation table. This step further confuses the data.
- XOR and Swap: The 32-bit output from the P-box step is XORed with the 32-bit left half of the plaintext block obtained from the initial permutation step. Then, the left and right halves of the data are swapped.
- Repeat: The above steps are repeated for a total of 16 rounds, with each round using a different subkey generated in the key generation step.
- Final Permutation (IP-1): After the 16 rounds of encryption, the resulting ciphertext block is subjected to a final permutation (IP-1) step, which is the inverse of the initial permutation step. This produces the final 64-bit ciphertext block.
(c) Explain Key Expansion in AES algorithm.
Key Expansion is a crucial step in the Advanced Encryption Standard (AES) algorithm, which is a symmetric key block cipher algorithm used for encryption and decryption of data. Key Expansion is performed to generate a set of round keys from the original secret key, which are used in each round of the AES algorithm.
The Key Expansion step in AES can be summarized as follows:
- Key Input: The original secret key is input into the AES algorithm. The size of the key can be 128, 192, or 256 bits, denoted as AES-128, AES-192, and AES-256, respectively.
- Key Schedule: The Key Expansion step generates a set of round keys, denoted as W[0], W[1], …, W[Nk*(Nr+1)], where Nk is the number of 32-bit words in the original secret key (4 words for AES-128, 6 words for AES-192, and 8 words for AES-256), and Nr is the number of rounds in the AES algorithm (10 rounds for AES-128, 12 rounds for AES-192, and 14 rounds for AES-256).
- Key Generation: The Key Expansion step uses a combination of bitwise XOR, substitution, and rotation operations to generate the round keys. The specific steps are as follows:a) Word Expansion: The 128-bit original secret key is divided into Nk words of 32 bits each. These words are used as the initial round keys W[0], W[1], …, W[Nk-1].b) Round Constants: A set of round constants denoted as Rcon[i], where i is the round number (starting from 1), is used in the key generation process. These round constants are predefined values that are XORed with one of the words in the previous round key to introduce variability in the generated round keys.c) Substitution: Each word in the round key is subjected to a byte-wise substitution using the AES S-box, which is a fixed substitution table.d) Rotation: For AES-192 and AES-256, after the substitution step, the bytes in the second word and subsequent words in the round key are rotated by one or two bytes, respectively.e) XOR: Each word in the round key is XORed with a corresponding word from the original secret key or the previous round key, and the round constants are XORed with the first word in the round key.
- Round Keys: The resulting set of round keys W[0], W[1], …, W[Nk*(Nr+1)] are used in each round of the AES algorithm, where each round key is used in XOR operations with the plaintext data or the intermediate data during encryption or decryption.
(a) Differentiate conventional encryption and public key encryption.
Conventional encryption and public key encryption are two different methods of encrypting data, and they differ in how they use keys for encryption and decryption:
- Key Usage: Conventional encryption, also known as symmetric key encryption, uses the same secret key for both encryption and decryption. This means that the same key is used to encrypt the plaintext data and then used again to decrypt the ciphertext back into plaintext. On the other hand, public key encryption, also known as asymmetric key encryption, uses a pair of keys – a public key and a private key. The public key is used for encryption, and the private key is used for decryption.
- Key Distribution: In conventional encryption, the same secret key used for encryption and decryption must be securely shared between the communicating parties before they can exchange encrypted messages. This can be challenging in terms of key management and distribution, especially in large-scale communication networks. In public key encryption, each user has a unique key pair consisting of a public key and a private key. The public key can be freely shared with anyone, while the private key must be kept secret. This allows for secure communication without the need for pre-shared keys.
- Encryption/Decryption Process: In conventional encryption, the same secret key is used for both encryption and decryption. The plaintext data is encrypted using the secret key with a symmetric encryption algorithm, and the resulting ciphertext is decrypted back into plaintext using the same secret key. In public key encryption, the public key is used for encryption and the private key is used for decryption. The plaintext data is encrypted using the recipient’s public key with an asymmetric encryption algorithm, and the resulting ciphertext can only be decrypted using the recipient’s private key.
- Security: In conventional encryption, the security of the encrypted data relies solely on the secrecy of the shared secret key. If the secret key is compromised or intercepted, the encrypted data may be vulnerable to decryption attacks. In public key encryption, the security relies on the secrecy of the private key, which is kept by the owner and not shared with anyone. The public key can be freely shared without compromising the security of the encrypted data. Public key encryption also provides additional functionalities such as digital signatures and authentication, which are not present in conventional encryption.
- Scalability: Conventional encryption may face challenges in terms of scalability and key management, especially in large-scale communication networks with a large number of users. Public key encryption provides a scalable solution as each user has a unique key pair, and the public keys can be freely shared without the need for pre-shared keys.
(b) In a public key system using RSA, the cipher text intercepted is C=12
which is sent to the user whose public key is e=5, n=35. What is the
plaintext M?
To find the plaintext message (M) from the given ciphertext (C), and the public key (e) and modulus (n) in an RSA public key system, we can use the following formula for RSA decryption:
M = C^d mod n
where: C = Ciphertext M = Plaintext message d = Private key (decryption key) n = Modulus e = Public key (encryption key)
To calculate the private key (d), we need to use the formula:
d = e^(-1) mod phi(n)
where phi(n) is the Euler’s totient function, which is calculated as:
phi(n) = (p – 1)(q – 1)
where p and q are the prime numbers used to generate the modulus n.
Given: C = 12 e = 5 n = 35
We can calculate phi(n) as follows: phi(n) = (p – 1)(q – 1) = (5 – 1)(7 – 1) = 4 * 6 = 24
Next, we can calculate the private key (d) as follows: d = e^(-1) mod phi(n) = 5^(-1) mod 24
To find the modular inverse of 5 mod 24, we can use a modular inverse calculator or use the Extended Euclidean Algorithm to compute it manually. In this case, we can see that 5 * 5 = 25, which is congruent to 1 modulo 24. Therefore, the modular inverse of 5 mod 24 is 5.
So, we have: d = 5
Now, we can use the private key (d) to decrypt the ciphertext (C) and obtain the plaintext message (M): M = C^d mod n = 12^5 mod 35
We can calculate the value of M using the exponentiation by squaring method, as follows: 12^2 mod 35 = 144 mod 35 = 9 9^2 mod 35 = 81 mod 35 = 11 11^2 mod 35 = 121 mod 35 = 16 16^2 mod 35 = 256 mod 35 = 11
So, the plaintext message (M) is 11.
(c) Explain SHA1 hashing algorithm in detail.
SHA-1 (Secure Hash Algorithm 1) is a cryptographic hash function that is widely used for generating fixed-size, 160-bit (20-byte) hash values from input data of arbitrary size. It was developed by the National Security Agency (NSA) in 1993 as part of the Secure Hash Standard (SHS) and is considered one of the most commonly used hash functions.
SHA-1 works by taking an input message and processing it through a series of mathematical operations to generate a fixed-size hash value that is unique to the input data. The hash value is typically represented as a hexadecimal string of 40 characters (160 bits).
The steps involved in the SHA-1 algorithm are as follows:
- Padding: The input message is first padded to ensure it has a length that is a multiple of 512 bits (the block size of SHA-1). The padding is done by adding bits in a specific pattern to the end of the input message.
- Message Digest Initialization: The initial hash values, denoted as H0, H1, H2, H3, and H4, are set as predetermined constants. These constants are used as the initial state of the hash function.
- Message Digest Computation: The padded input message is divided into blocks of 512 bits each. Each block is then processed in a series of rounds to update the hash values.
- Round Operations: Each round of the SHA-1 algorithm involves several operations, including bitwise logical operations (such as AND, OR, XOR), modular arithmetic, and bit rotation operations. These operations are performed on the current hash values and the data from the current block being processed.
- Final Hash Value: After processing all the blocks of the input message, the resulting hash values (H0, H1, H2, H3, and H4) are combined to form the final hash value, which is the output of the SHA-1 algorithm.
OR
(a) Alice meets Bob and says “Wshu H pz uva dvyrpun wyvwlysf. dl ohcl
av tvcl av aol wshu I.” If she is using Caesar Cipher, what does she want
to convey?
Alice is using the Caesar Cipher to encrypt her message to Bob. The encrypted message “Wshu H pz uva dvyrpun wyvwlysf. dl ohcl av tvcl av aol wshu I” can be decoded using a Caesar Cipher with a left shift of 7 (assuming a standard English alphabet with 26 letters).
Decoding the message using a Caesar Cipher with a left shift of 7, we get the original plaintext message:
“This C is not something meaningful. by this my name my the way I.”
So, the decrypted message is: “This C is not something meaningful. by this my name my the way I.”
Alice is trying to convey the message: “This is not something meaningful. By the way, my name is the way I.”
(b) User A & B exchange the key using Diffie Hellman algorithm Assume
public numbers P=17 G=2 and private values X=3 Y=7 respectively.
Find the Public Value R1,R2 and key K of user A and B.
Public numbers: P = 17 G = 2
Private values: User A: X = 3 User B: Y = 7
- User A computes the public value R1: R1 = G^X mod P R1 = 2^3 mod 17 R1 = 8 mod 17 So, R1 = 8 is the public value of User A.
- User B computes the public value R2: R2 = G^Y mod P R2 = 2^7 mod 17 R2 = 128 mod 17 So, R2 = 13 is the public value of User B.
- User A and User B exchange R1 and R2 over a secure channel.
- User A computes the shared secret key K: K = R2^X mod P K = 13^3 mod 17 K = 2197 mod 17 So, K = 4 is the shared secret key of User A.
- User B computes the shared secret key K: K = R1^Y mod P K = 8^7 mod 17 K = 2097152 mod 17 So, K = 2 is the shared secret key of User B.
Now, User A and User B have successfully exchanged the secret key using the Diffie-Hellman algorithm. The shared secret key K for User A is 4, and the shared secret key K for User B is 2.
(c) Describe MAC? Explain HMAC algorithm in details.
A Message Authentication Code (MAC) is a cryptographic technique that provides integrity and authenticity of a message. It is a short piece of information, typically a fixed-size, that is appended to the message to verify the authenticity of the message.
The MAC algorithm takes a secret key and a message as inputs and generates a fixed-size MAC tag as an output. The MAC tag is then transmitted along with the message to the receiver. Upon receiving the message and MAC tag, the receiver recalculates the MAC tag using the same algorithm, and if the recalculated MAC tag matches the transmitted MAC tag, then the message is considered authentic.
The HMAC (Hashed Message Authentication Code) algorithm is a widely used MAC algorithm. It combines two cryptographic primitives: a cryptographic hash function and a secret key.
The HMAC algorithm works as follows:
- Define the message M and the secret key K.
- Choose a cryptographic hash function H (such as SHA-256, SHA-384, or SHA-512) that outputs a fixed-size hash value.
- Apply a key derivation function to the secret key K to obtain two derived keys, K1 and K2.
- If the hash function H outputs a hash value that is the same size as the key K (e.g., H is SHA-256 and K is 256 bits), then K1 and K2 can be obtained as follows: K1 = K XOR (0x5c * 16) K2 = K XOR (0x36 * 16)
- Otherwise, if the hash function H outputs a hash value that is larger than the key K, then K1 and K2 can be obtained as follows: K1 = H(K XOR (0x5c * 16)) K2 = H(K XOR (0x36 * 16))
- Calculate the inner hash value by applying the hash function H to the concatenation of K1 and the message M: InnerHash = H(K1 || M)
- Calculate the outer hash value by applying the hash function H to the concatenation of K2 and the inner hash value: OuterHash = H(K2 || InnerHash)
- The resulting HMAC tag is the outer hash value: HMAC = OuterHash
(a) List and explain transposition techniques in cryptography.
Transposition techniques in cryptography refer to methods of encrypting plaintext by rearranging the positions of its characters or symbols without altering their identities. Transposition techniques do not change the actual characters or symbols of the plaintext but rather change their order, making them suitable for achieving confidentiality in data communication.
Here are some common transposition techniques in cryptography:
- Columnar Transposition: In this technique, the plaintext is written in rows of fixed-length columns, and then the columns are rearranged according to a specific key or permutation rule. The ciphertext is obtained by reading the columns row-wise. Columnar transposition can be done with or without a keyword. It provides moderate security and is relatively simple to implement.
- Rail Fence: In this technique, the plaintext is written diagonally on successive “rails” or lines, and then the characters are read off row-wise to obtain the ciphertext. The number of rails used determines the level of encryption. Rail fence is easy to implement, but it may not provide strong security as it can be susceptible to frequency analysis attacks.
- Route Transposition: Also known as the “Scytale” cipher, this technique involves wrapping the plaintext around a cylinder of a fixed circumference and then reading it off in a different order, typically in a spiral or zigzag pattern. The ciphertext is obtained by reading the characters from the cylinder in the order specified by the route. Route transposition provides moderate security and can be implemented in various ways.
- Double Transposition: This technique combines two or more rounds of transposition using different methods. For example, a columnar transposition followed by a row transposition or vice versa. Double transposition can provide increased security compared to single transposition techniques.
- Myszkowski Transposition: In this technique, the plaintext is arranged in a matrix and then rearranged according to a specific rule, such as the positions of repeating characters. The ciphertext is obtained by reading off the columns row-wise. Myszkowski transposition can provide stronger security compared to other transposition techniques, but it may require more complex implementation.
(b) Write the Euclid’s algorithm and show the steps of Euclid’s algorithm
to find gcd(401,700).
Euclid’s algorithm is a widely used algorithm for finding the greatest common divisor (GCD) of two positive integers. It is based on the principle that the GCD of two numbers is the same as the GCD of the smaller number and the remainder obtained when the larger number is divided by the smaller number. Here are the steps of Euclid’s algorithm to find gcd(401,700):
Step 1: Start with the given numbers, 401 and 700.
Step 2: Divide the larger number by the smaller number and find the remainder. 700 ÷ 401 = 1 with a remainder of 298
Step 3: Replace the larger number with the smaller number and the smaller number with the remainder obtained in the previous step. 401 ÷ 298 = 1 with a remainder of 103
Step 4: Repeat step 2 and step 3 until the remainder becomes 0. 298 ÷ 103 = 2 with a remainder of 92 103 ÷ 92 = 1 with a remainder of 11 92 ÷ 11 = 8 with a remainder of 8 11 ÷ 8 = 1 with a remainder of 3 8 ÷ 3 = 2 with a remainder of 2 3 ÷ 2 = 1 with a remainder of 1 2 ÷ 1 = 2 with no remainder
Step 5: The last non-zero remainder obtained in the previous step is the GCD of the given numbers, which in this case is 1.
So, gcd(401,700) = 1 according to Euclid’s algorithm.
(c) Describe the principle of digital signature algorithm (DSA).Explain the
signing and verifying function in DSA.
The Digital Signature Algorithm (DSA) is a widely used asymmetric cryptographic algorithm for creating and verifying digital signatures, which are used for ensuring the integrity, authenticity, and non-repudiation of digital data. DSA uses a pair of keys, a private key for signing and a public key for verifying, to provide secure digital signatures.
The principle of DSA is based on the concept of discrete logarithm, which is a mathematical problem that is believed to be computationally hard to solve. DSA involves the use of a large prime number and modular arithmetic operations to generate the keys and create digital signatures.
Signing Function in DSA:
- Key Generation: A user generates a pair of keys – a private key (x) and a public key (y) – using DSA key generation algorithm. The private key (x) is kept secret, while the public key (y) is shared with others.
- Hashing: The user computes the hash value (H) of the message to be signed using a cryptographic hash function. The hash function generates a fixed-size hash value from the input message, which serves as a fingerprint of the message.
- Signature Generation: The user computes the signature (r, s) of the hash value (H) using the private key (x) and the DSA signing algorithm. The signature consists of two values – r and s – which are calculated based on the hash value, the private key, and other parameters.
Verifying Function in DSA:
- Signature Extraction: A verifier receives the signed message along with the public key (y) and the signature (r, s).
- Hashing: The verifier computes the hash value (H) of the received message using the same cryptographic hash function that was used by the signer.
- Signature Verification: The verifier uses the DSA verification algorithm, along with the public key (y), the hash value (H), and the signature (r, s), to verify the authenticity of the signature. The verification process involves the calculation of values based on the parameters and the public key, and comparing them with the signature values (r, s). If the computed values match the signature values, the signature is considered valid, and the message is considered authentic and not tampered with.
OR
(a) Explain replaying attack with example.
A replay attack is a type of cyber attack where an attacker captures a legitimate data transmission and replays it later to gain unauthorized access or cause other malicious actions. This type of attack takes advantage of the lack of proper authentication and validation mechanisms in a system, allowing the attacker to replay previously captured data, such as network packets, authentication credentials, or other sensitive information.
Here’s an example of a replay attack:
Suppose Alice and Bob are communicating over a network using a simple authentication protocol. Alice sends a request to Bob to transfer $100 from her bank account to Bob’s account. To authenticate the request, Alice’s request includes her username, password, and a timestamp. Bob receives the request and validates the timestamp to ensure it is within an acceptable time window.
However, an attacker named Eve is eavesdropping on the network and captures Alice’s request, including her username, password, and timestamp. Eve then replays the captured request multiple times, within the valid time window, to Bob’s server.
Since Bob’s server does not have proper mechanisms to detect and prevent replay attacks, it processes each replayed request as a legitimate one. As a result, Bob’s server transfers $100 from Alice’s account to Bob’s account multiple times, as instructed by the replayed requests. This allows Eve to fraudulently transfer $100 from Alice’s account to Bob’s account multiple times, without proper authorization.
(b) Describe Elgamal digital signature.
ElGamal digital signature is a type of asymmetric cryptographic algorithm used for creating and verifying digital signatures. It is based on the ElGamal encryption algorithm, which was developed by Taher ElGamal in 1984 and is widely used for secure communications and digital signatures.
The ElGamal digital signature algorithm involves a pair of keys, a private key for signing and a public key for verifying, similar to other asymmetric cryptographic algorithms. The algorithm is typically used with a hash function to create a digital signature that provides integrity, authenticity, and non-repudiation of digital data.
Here’s an overview of how the ElGamal digital signature algorithm works:
- Key Generation: A user generates a pair of keys – a private key (x) and a public key (y) – using the ElGamal key generation algorithm. The private key (x) is kept secret, while the public key (y) is shared with others.
- Signature Generation:
- Hashing: The user computes the hash value (H) of the message to be signed using a cryptographic hash function. The hash function generates a fixed-size hash value from the input message, which serves as a fingerprint of the message.
- Random Number Generation: The user generates a random number (k) within a certain range.
- Calculation: The user calculates the signature (r, s) using the private key (x), the hash value (H), and the random number (k) according to the ElGamal signature algorithm formulas:
- r = (g^k) mod p, where g is a generator of a multiplicative group modulo p, and p is a large prime number.
- s = (k^(-1))(H – xr) mod (p-1), where k^(-1) is the modular multiplicative inverse of k modulo (p-1), and xr is the modular multiplication of x and r modulo (p-1).
- Signature Verification:
- Hashing: The verifier computes the hash value (H) of the received message using the same cryptographic hash function that was used by the signer.
- Calculation: The verifier uses the public key (y), the hash value (H), and the signature (r, s) to verify the authenticity of the signature according to the ElGamal verification algorithm formulas:
- v = ((y^r)(r^s)) mod p, where y is the public key, r and s are the signature values.
- If v is equal to (g^H) mod p, the signature is considered valid and the message is considered authentic and not tampered with.
(c) Define KDC? With the help of diagram explain how KDC do key
distribution.
KDC stands for Key Distribution Center. It is a central entity in a network that is responsible for securely distributing keys for cryptographic operations, such as encryption, decryption, authentication, and integrity verification. KDC acts as a trusted third party that facilitates secure communication between entities in a network by generating and distributing cryptographic keys.
Here’s how KDC typically works for key distribution:
- Authentication: Entities in the network, often referred to as “principals,” need to authenticate themselves to the KDC before requesting keys. Authentication is usually done using a shared secret, such as a password or a digital certificate.
- Key Request: Once authenticated, a principal can request a key from the KDC for a specific cryptographic operation, such as encrypting a message or verifying the integrity of data.
- Key Generation: The KDC generates the requested key and encrypts it using the public key of the recipient principal. This ensures that only the recipient, who possesses the corresponding private key, can decrypt and obtain the key.
- Key Distribution: The encrypted key is then sent to the recipient principal. The recipient principal uses its private key to decrypt the encrypted key and obtain the shared key for the requested cryptographic operation.
- Secure Storage: The recipient principal securely stores the shared key for future use in cryptographic operations, such as encrypting or decrypting messages or verifying the integrity of data.
Here’s a simple diagram illustrating the key distribution process with a KDC:
+-------------+ +-------------+
| Principal A | | Principal B |
+-------------+ +-------------+
| |
| 1. Authentication |
|------------------------------> |
| |
| 2. Key Request |
|------------------------------> |
| |
| 3. Key Generation |
| <---------------------------- |
| |
| 4. Key Distribution |
|------------------------------> |
| |
| 5. Secure Storage |
| |
| Shared Key |
+--------------------------------+(a) What is the purpose of HTTPS?
HTTPS (HyperText Transfer Protocol Secure) is a secure version of the HTTP protocol that is used for communication between web browsers and web servers over the internet. The purpose of HTTPS is to provide secure and encrypted communication to protect sensitive data transmitted between a web browser and a web server.
The main purposes of HTTPS are:
- Data Confidentiality: HTTPS encrypts the data transmitted between the web browser and the web server, ensuring that it cannot be intercepted or viewed by unauthorized parties. This helps to protect sensitive information, such as credit card numbers, passwords, and personal information, from being intercepted by eavesdroppers.
- Data Integrity: HTTPS ensures that the data transmitted between the web browser and the web server is not tampered with during transmission. It uses message integrity checks, such as digital signatures, to detect any unauthorized modifications or alterations to the data.
- Authentication: HTTPS provides authentication of the web server, ensuring that the web browser is communicating with the legitimate server and not a fake or malicious server. This is typically done using digital certificates issued by trusted Certificate Authorities (CAs) that verify the identity of the web server.
- Trust and Confidence: HTTPS provides a visual indication to users that the website they are accessing is secure by displaying a padlock icon or a green address bar in the web browser. This helps to build trust and confidence among users that their data is being transmitted securely and that they are accessing a legitimate website.
(b) Write a short note on Secure Socket Layer.
Secure Socket Layer (SSL) is a cryptographic protocol that provides secure communication over the internet. It is commonly used to encrypt data transmitted between a web browser and a web server, ensuring that the data remains confidential and cannot be intercepted or tampered with by unauthorized parties.
SSL works by establishing a secure connection between the client (e.g., web browser) and the server (e.g., web server) through a series of handshakes and negotiations. During the SSL handshake, the client and server exchange cryptographic keys and establish a secure session, which is then used to encrypt data transmitted between them.
The main features of SSL include:
- Encryption: SSL uses cryptographic algorithms to encrypt data, ensuring that it remains confidential and secure during transmission. This prevents eavesdropping and data interception by unauthorized parties.
- Authentication: SSL provides server authentication, verifying the identity of the web server to the client. This helps to ensure that the client is communicating with the legitimate server and not a fake or malicious server.
- Integrity: SSL ensures that the data transmitted between the client and server remains unchanged during transmission. It uses message integrity checks, such as digital signatures, to detect any unauthorized modifications or alterations to the data.
- Trust and Confidence: SSL uses digital certificates issued by trusted Certificate Authorities (CAs) to authenticate the identity of the web server. This helps to build trust and confidence among users that they are accessing a legitimate website.
(c) Draw and explain Kerberos protocol in details.
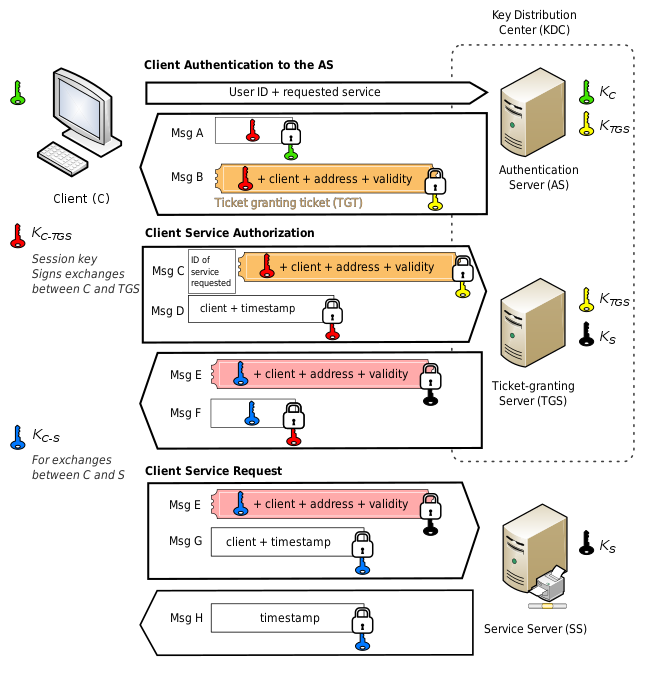
The Kerberos protocol is a widely used authentication protocol that provides secure authentication for client-server applications in a networked environment. It uses a trusted third-party entity known as the Key Distribution Center (KDC) to securely authenticate clients and servers, and establish session keys for secure communication. Here’s a step-by-step explanation of the Kerberos protocol:
- Pre-Authentication: The client authenticates itself to the KDC by sending its credentials, typically in the form of a username and password. This is called pre-authentication and helps to prevent unauthorized access to the KDC.
- Ticket Granting Ticket (TGT) Request: After successful pre-authentication, the client sends a request to the KDC for a Ticket Granting Ticket (TGT), which is a ticket that contains the client’s identity, the server’s identity, and a session key. The TGT is encrypted using the client’s password as a key and is sent back to the client.
- TGT Validation: The client decrypts the TGT using its password, which verifies the client’s identity. The client then stores the TGT securely and uses it to request service tickets without needing to re-authenticate to the KDC.
- Service Ticket Request: When the client wants to access a specific service on a server, it sends a request to the KDC for a service ticket. The request includes the TGT, the client’s identity, and the server’s identity.
- Service Ticket Issuance: The KDC verifies the TGT, the client’s identity, and the server’s identity. If the request is valid, the KDC issues a service ticket to the client. The service ticket contains the client’s identity, the server’s identity, and a session key for secure communication with the server.
- Service Ticket Presentation: The client presents the service ticket to the server as proof of authentication. The server verifies the service ticket, the client’s identity, and the server’s identity. If all the information matches, the server grants access to the requested service.
- Session Key Establishment: Upon successful authentication, the client and the server use the session key from the TGT or service ticket to establish a secure session for communication. This session key is unique for each client-server pair and is used to encrypt and decrypt data exchanged between them.
- Renewal and Expiration: The TGT and service tickets have a limited validity period. The client can request TGT renewal from the KDC to extend the session duration, or request a new TGT after the current one expires. This helps to maintain the security of the system by limiting the lifespan of tickets and session keys.
OR
(a) Define Following Terms:
i) Group
ii) Ring
iii) Field
i) Group: In abstract algebra, a group is a set G equipped with an operation * that satisfies four main properties: closure, associativity, identity, and inverse.
Closure: For any two elements a, b in G, their product a * b is also in G.
Associativity: For any three elements a, b, c in G, the operation * satisfies the associative property, meaning that (a * b) * c = a * (b * c).
Identity: There exists an element e in G, called the identity element, such that for any element a in G, a * e = e * a = a.
Inverse: For any element a in G, there exists an element b in G, called the inverse of a, such that a * b = b * a = e, where e is the identity element of G.
Groups have many applications in various areas of mathematics, computer science, and cryptography, and they are used to describe mathematical structures with specific properties.
ii) Ring: In abstract algebra, a ring is a set R equipped with two operations, usually denoted as addition (+) and multiplication (*), that satisfy certain properties.
Addition: The operation (+) makes R into an abelian group, meaning that it satisfies the properties of closure, associativity, identity (0 is the additive identity), and inverse (each element has an additive inverse).
Multiplication: The operation (*) satisfies the properties of closure, associativity, and distributivity over addition. However, multiplication in a ring may not have an identity element, and it may not necessarily be commutative (i.e., a * b may not always equal b * a).
Rings are commonly used in algebra, number theory, and computer science, and they provide a general framework for studying structures that have both addition and multiplication operations.
iii) Field: In abstract algebra, a field is a set F equipped with two operations, addition (+) and multiplication (*), that satisfy the properties of a ring, with the additional requirement that every non-zero element of F has a multiplicative inverse.
Addition: The operation (+) makes F into an abelian group, meaning that it satisfies the properties of closure, associativity, identity (0 is the additive identity), and inverse (each element has an additive inverse).
Multiplication: The operation (*) satisfies the properties of closure, associativity, distributivity over addition, and also has an identity element (1 is the multiplicative identity). Additionally, every non-zero element of F has a multiplicative inverse, meaning that for any non-zero element a in F, there exists an element b in F such that a * b = b * a = 1.
(b) Explain Public key Infrastructure in security.
Public Key Infrastructure (PKI) is a set of policies, procedures, and technologies that are used to manage the creation, distribution, usage, and revocation of digital certificates, which are used to secure communications and authenticate users in a networked environment. PKI is a fundamental building block of modern security systems, including those used in secure communication over the internet, such as SSL/TLS for secure web browsing, email encryption, and digital signatures.
PKI relies on the use of public key cryptography, which involves the use of key pairs: a public key and a private key. The public key is made publicly available, while the private key is kept securely by the owner. These keys are mathematically related, such that data encrypted with one key can only be decrypted with the corresponding key from the key pair.
PKI consists of the following main components:
- Certificate Authority (CA): A CA is a trusted entity that issues digital certificates to entities (such as users, devices, or servers) after verifying their identity. The CA signs the digital certificates using its private key, which is known only to the CA, to ensure the integrity and authenticity of the certificates. CAs can be hierarchical, with one or more root CAs at the top of the hierarchy, followed by intermediate CAs, and end-entity CAs that issue certificates to individual entities.
- Digital Certificates: A digital certificate is a digital document that binds an entity’s public key to its identity. It contains information such as the entity’s name, public key, validity period, and the CA’s signature. Digital certificates are used for authentication, encryption, and digital signatures.
- Public Key Infrastructure (PKI) Policies: PKI policies are a set of rules and procedures that govern the issuance, management, and revocation of digital certificates. PKI policies define the trust model, authentication procedures, and other security-related aspects of the PKI.
- Certificate Revocation: PKI includes mechanisms for certificate revocation, which allow a CA to revoke a certificate before its expiration date. This can happen in case of compromise of the private key, change in the entity’s status, or other security reasons.
PKI provides several security benefits, including:
- Authentication: PKI enables the verification of the identity of entities in a networked environment, helping to establish trust and ensure that communications are secure.
- Confidentiality: PKI supports the use of encryption, allowing for secure communication and data transfer between entities.
- Integrity: PKI ensures the integrity of digital certificates through the use of digital signatures, which provide a tamper-proof means of verifying the authenticity of certificates.
- Non-repudiation: PKI enables the use of digital signatures, which provide proof of origin and integrity of digital data, helping to prevent repudiation or denial of actions or transactions.
- Scalability: PKI provides a scalable framework for managing large numbers of entities and digital certificates in a networked environment.
(c) Explain X.509 authentication service.
Public Key Infrastructure (PKI) is a set of policies, procedures, and technologies that are used to manage the creation, distribution, usage, and revocation of digital certificates, which are used to secure communications and authenticate users in a networked environment. PKI is a fundamental building block of modern security systems, including those used in secure communication over the internet, such as SSL/TLS for secure web browsing, email encryption, and digital signatures.
PKI relies on the use of public key cryptography, which involves the use of key pairs: a public key and a private key. The public key is made publicly available, while the private key is kept securely by the owner. These keys are mathematically related, such that data encrypted with one key can only be decrypted with the corresponding key from the key pair.
PKI consists of the following main components:
- Certificate Authority (CA): A CA is a trusted entity that issues digital certificates to entities (such as users, devices, or servers) after verifying their identity. The CA signs the digital certificates using its private key, which is known only to the CA, to ensure the integrity and authenticity of the certificates. CAs can be hierarchical, with one or more root CAs at the top of the hierarchy, followed by intermediate CAs, and end-entity CAs that issue certificates to individual entities.
- Digital Certificates: A digital certificate is a digital document that binds an entity’s public key to its identity. It contains information such as the entity’s name, public key, validity period, and the CA’s signature. Digital certificates are used for authentication, encryption, and digital signatures.
- Public Key Infrastructure (PKI) Policies: PKI policies are a set of rules and procedures that govern the issuance, management, and revocation of digital certificates. PKI policies define the trust model, authentication procedures, and other security-related aspects of the PKI.
- Certificate Revocation: PKI includes mechanisms for certificate revocation, which allow a CA to revoke a certificate before its expiration date. This can happen in case of compromise of the private key, change in the entity’s status, or other security reasons.
PKI provides several security benefits, including:
- Authentication: PKI enables the verification of the identity of entities in a networked environment, helping to establish trust and ensure that communications are secure.
- Confidentiality: PKI supports the use of encryption, allowing for secure communication and data transfer between entities.
- Integrity: PKI ensures the integrity of digital certificates through the use of digital signatures, which provide a tamper-proof means of verifying the authenticity of certificates.
- Non-repudiation: PKI enables the use of digital signatures, which provide proof of origin and integrity of digital data, helping to prevent repudiation or denial of actions or transactions.
- Scalability: PKI provides a scalable framework for managing large numbers of entities and digital certificates in a networked environment.
“Do you have the answer to any of the questions provided on our website? If so, please let us know by providing the question number and your answer in the space provided below. We appreciate your contributions to helping other students succeed.”
